|
Phone: (203) 748-2960 (Danbury, CT) E-mail: David Mawdsley |
|
Phone: (203) 748-2960 (Danbury, CT) E-mail: David Mawdsley |
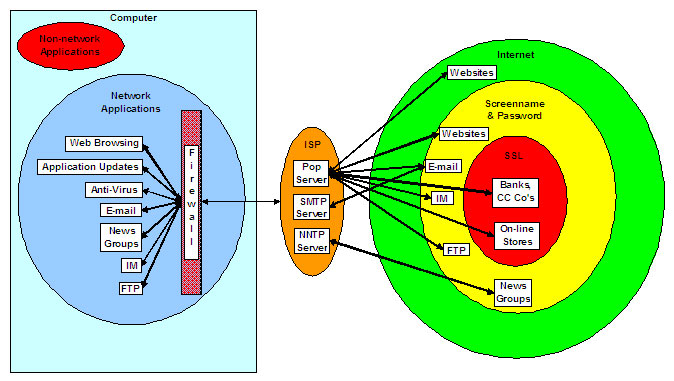
| The figure shows a computer connected via an Internet Service Provider (ISP) to the Internet in various ways.
The computer uses ports which the firewall will either allow or disallow for traffic by the various applications. What is noticeable is that much of the connections to the Internet are not encrypted and thus leaving open vulnerabilities. After logging into the ISP with a screenname and a password (Orange), most web browsing, is not encrypted and does not require further loggin in. (Green) Be very selective about clicking on links or buttons on sites here. Once at a website a click on a malicious link could cause adware or spyware to download and install on the computer. Occasionally websites will require a second authentication to view webpages or use an information transfer of some sort, but once the user has logged on, the site is unencrypted. (Yellow) Thus any intercepted data is in clear text and could be read. Only when a site is fully using the Secure Socket Layer (SSL) will the data traffic between the website and the computer be fully encrypted for the duration of the session. Thus even if the data is intercepted, it can't be decyphered. Users usually log out after using an encrypted site. (Red) Look for the webpage address, its URL, to start with https:// . A lock symbol should also be in a corner of the screen. Sites using SSL involve banking and purchases using credit cards--private, sensitive, personal information.
|